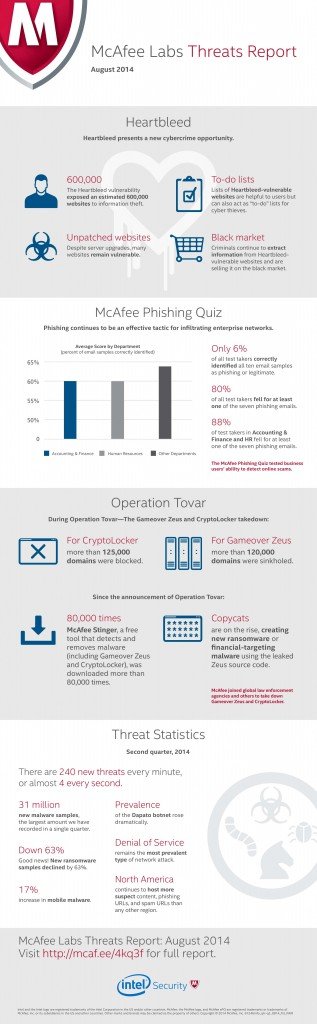
McAfee Labs today released the McAfee Labs Threats Report: August 2014, revealing that phishing continues to be an effective tacticfor infiltrating enterprise networks. Testing business users’ ability to detect online scams, the McAfee Phishing Quiz uncovered that 80% of its participants failed to detect at least one of seven phishing emails. Furthermore, results showed that finance and HR departments, those holding some of the most sensitive corporate data, performed the worst at detecting scams, falling behind by a margin of 4% to 9%.
Check out the infographic below:
Around the world, the ability to detect phishing varied by region. EMEA proved to be the most skilled at an average of 67% correct. Bahrain, United Arab Emirates, and Saudi Arabia were among the 48 countries participating in the McAfee Phishing Quiz in the EMEA region.
Since last quarter’s Threats Report, McAfee Labs has collected more than 250,000 new phishing URLs, leading to a total of nearly one million new sites in the past year. Not only was there an increase in total volume, there was a significant rise in the sophistication of phishing attacks occurring in the wild. Results showed both mass campaign phishing and spear phishing are still rampant in the attack strategies used by cybercriminals around the world. Meanwhile, the United States continues to host more phishing URLs than any other country.
In the ME region the countries hosting phishing URLs are the UAE: 7 domains, KSA: 5 domains, Palestine: 3 domains, Syria and Lebanon: 2 domains each, Jordan, Iraq and Kuwait: 1 domain each.
“Despite being among the best in detecting phishing emails and hosting lesser phishing domains in comparison to other parts of the world, the ME region remains one of the most vulnerable regions to cyber security breaches. It takes only one infected email to deliver malware and cause damage. This is why it remains essential to educate users on best practices in detecting and acting upon suspicious emails,” said Hamed Diab, McAfee’s regional director in the Middle East and North Africa.
Findings also revealed new cybercrime opportunities since the public disclosure of the Heartbleed vulnerability, as stolen data from still vulnerable websites is currently being sold on the black market. Lists of unpatched websites have quickly become hit lists for cybercriminals and tools are readily available to mine unpatched sites. With these tools, it is possible to tie together an automated system that targets known vulnerable machines and extracts sensitive information.
“One of the great challenges we face today is upgrading the Internet’s core technologies to better suit the volume and sensitivity of traffic it now bears,” said Vincent Weafer, senior vice president for McAfee Labs. “Every aspect of the trust chain has been broken in the last few years—from passwords to OpenSSL public key encryption and most recently USB security. The infrastructure that we so heavily rely on depends on technology that hasn’t kept pace with change and no longer meets today’s demands.”
Each quarter, the McAfee Labs team of more than 400 multidisciplinary researchers in 30 countries follows the complete range of threats in real time, identifying application vulnerabilities, analyzing and correlating risks, and enabling instant remediation to protect enterprises and the public.
Additional Key Findings
- Operation Tovar: McAfee joined global law enforcement agencies and others to take down Gameover Zeus and CryptoLocker by blocking more than 125,000 CryptoLocker domains and sinkholing in excess of 120,000 Gameover Zeus domains. However, copycats are on the rise, creating new variants of ransomware or financial-targeting malware using the leaked Zeus source code.
- Growth in Malware: New malware samples rose by only 1% in the second quarter. However, with more than 31 million new samples, this was still the largest amount recorded in a single quarter. The total count of mobile malware increased by 17% in the second quarter, while the rate of new mobile malware appears to have leveled off at about 700,000 per quarter.
- Network Threats: Denial of service attacks rose by 4% in the second quarter and remain the most prevalent type of network threat.